Server
security.xml
Change all SSL configs in security.xml to TLSv1.2 in all profiles including deployment manager profile
/opt/IBM/WebSphere/AppServer/profiles/AppSrv01/config/cells/VPS1Cell01
/opt/IBM/WebSphere/AppServer/profiles/Dmgr01/config/cells/VPS1Cell01
Sample
*Make this change for all SSL configs defined in the file
<repertoire xmi:id=”SSLConfig_2″ alias=”NodeDefaultSSLSettings” managementScope=”ManagementScope_3″>
<setting xmi:id=”SecureSocketLayer_3″ clientAuthentication=”false” securityLevel=”HIGH” enabledCiphers=”” jsseProvider=”IBMJSSE2″ ssl
Protocol=”TLSv1.2” keyStore=”KeyStore_7″ trustStore=”KeyStore_2″ trustManager=”TrustManager_2″ keyManager=”KeyManager_1″>
<properties xmi:id=”Property_1529890233660″ name=”com.ibm.ssl.changed” value=”4″/>
</setting>
</repertoire>
ssl.client.props
Change all SSL protocol in ssl.client.xml to TLSv1.2 in all profiles including deployment manager profile
/opt/IBM/WebSphere/AppServer/profiles/AppSrv01/properties
/opt/IBM/WebSphere/AppServer/profiles/Dmgr01/properties
Sample
com.ibm.ssl.protocol=TLSv1.2
Restart
Restart Deployment manager, node agents and nodes.
Client
IBM MDM BatchProcessor
If BatchProcessor could not connect to MDM instance after upgrading to TLSv1.2, change SSL protocol in ssl.client.props to TLSv1.2 in all BatchProcessor instances.
/opt/IBM/MDM/BatchProcessor/properties
Sample
com.ibm.ssl.protocol=TLSv1.2
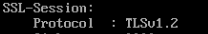
Validation
Shell
openssl s_client -connect <hostname>:<secure port>